Table Of Contents
Skimming Fraud Meaning
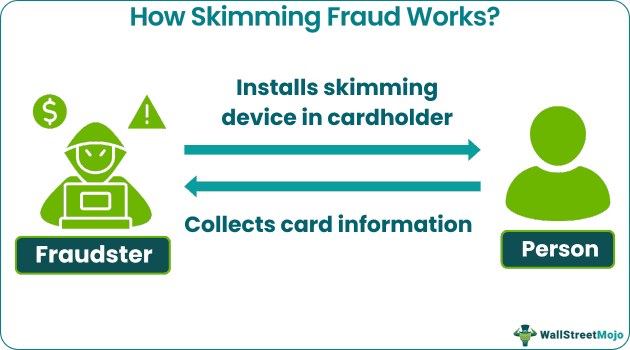
Skimming Fraud refers to a type of financial crime where criminals obtain unauthorized access to credit or debit card information by installing illegal card-reading devices (skimmers) on legitimate payment terminals, ATMs, or other point-of-sale devices. These skimmers capture the card data of unsuspecting users when they make transactions.
It is a serious problem due to its potential to compromise individuals' financial security by enabling unauthorized transactions. One requires heightened awareness and security to detect and prevent skimming, safeguarding individuals from fraudulent activities and protecting the integrity of electronic payment systems.
Table of contents
- Skimming Fraud Meaning
- Skimming fraud refers to the illegal practice of collecting personal or financial information from payment cards (e.g., credit cards, debit cards) without the knowledge or consent of the cardholder.
- The fraudster typically does this using skimming devices or techniques, which they can place on legitimate card readers (like ATMs, gas pumps, or point-of-sale terminals) or through handheld devices.
- To prevent skimming fraud, be cautious when using payment cards, use secure and trusted card readers, and regularly monitor your account activity for suspicious transactions.
Skimming Fraud Explained
Skimming fraud is a form of financial fraud that involves the unauthorized collection of credit or debit card information from unsuspecting individuals. It typically occurs at legitimate payment terminals, ATMs (Automated Teller Machines), or other point-of-sale devices. The main objective of the fraudsters is to steal the card data, including the cardholder's name, card number, expiration date, and sometimes the PIN (Personal Identification Number).
Here's how skimming fraud generally works:
- Skimmer Installation: The fraudsters physically install a device called a skimmer on top of or inside the legitimate card reader. The skimmer often looks like a regular card reader, making it hard for users to notice it.
- Data Capture: When a person inserts their card into the compromised payment terminal, the skimmer reads and records the magnetic stripe data from the card. Some skimmers may also use hidden cameras or keypad overlays to capture the PIN entered by the user.
- Data Retrieval: The fraudsters later return to the compromised terminal to retrieve the skimming device or remotely access the stored data. Alternatively, they may use Bluetooth or other wireless technology to transfer the stolen data to their devices.
- Counterfeit Card Creation: With stolen card data, criminals can create counterfeit cards using blank cards with magnetic stripes or EMV (Europay, Mastercard and Visa) chips. The counterfeit cards will have the same information as the original cards, allowing them to make unauthorized transactions.
- Unauthorized Transactions: The criminals use counterfeit cards to make purchases, withdrawals, or other transactions, often in different locations or countries, to avoid detection.
- Victim Realization: The victim typically becomes aware of the fraudulent activity when they notice unauthorized transactions on their bank or credit card statements or when their card is unexpectedly declined due to suspicious activity.
The Hargreaves Lansdown provides access to a range of investment products and services for UK investors.
Types
Skimming fraud can take several forms, each targeting different types of payment methods and devices. Here are some common types of skimming fraud:
- ATM Skimming: Criminals place skimming devices on ATMs to capture card information from unsuspecting users. These devices may be overlay skimmers on the card slot, hidden cameras to record PINs, or even fake keypads placed on top of the real one.
- Gas Pump Skimming: Fraudsters install skimmers on gas station pumps to steal credit and debit card data from customers making payments at the pump. Like ATM skimming, these can include card readers or hidden cameras.
- Point-of-Sale (POS) Skimming: Skimmers can be placed on payment terminals in retail stores, restaurants, or other places where customers make card transactions. This type of skimming aims to collect card data when customers make purchases.
- E-commerce Skimming (Magecart Attacks): In this digital form of skimming, hackers compromise websites by injecting malicious code into their payment pages. When customers enter their card information during online transactions, the criminals intercept data and steal it.
- Card Reader Overlay Skimming: Criminals place realistic-looking skimming devices on top of legitimate card readers in ATMs, ticket kiosks, or payment terminals. These overlays capture the card data when users insert their cards.
Examples
Let us look at the skimming fraud examples to understand the concept better -
Example #1
Suppose in a quaint tourist town, a popular ice cream parlor becomes the target of skimming fraud. Unscrupulous individuals discreetly install skimming devices on the shop's card reader, blending them seamlessly with the original equipment. As families and vacationers flock to the parlor for sweet treats, their credit card information is unknowingly compromised during transactions. The fraudsters quickly gather the stolen data and create counterfeit cards.
With these cloned cards, they make unauthorized purchases at nearby shops and online retailers. It is not until weeks later that customers notice mysterious charges on their bank statements. Suspecting foul play, they report the incidents to local authorities, prompting an investigation. Through diligent surveillance footage analysis, law enforcement identifies the skimming culprits and apprehends them, warning both businesses and visitors of the ever-present risk of skimming fraud.
Example #2
One real-life historical example of skimming fraud is the Operation Get Rich or Die Tryin case in the United States in the mid-2000s.
The case involved a group of criminals in an elaborate skimming scheme targeting various casinos in Las Vegas, Nevada. The perpetrators installed hidden cameras and skimming devices on the card readers of slot machines and ATMs within the casinos.
Here is how the skimming fraud operation unfolded:
- Skimmer Placement: The fraudsters gained access to the casinos, often posing as regular patrons or employees. They strategically installed skimming devices on the card readers of slot machines and ATMs located in the casinos' gambling areas.
- Data Collection: The skimming devices captured the card information of unsuspecting casino visitors who used their credit or debit cards to withdraw cash from ATMs or play slot machines. The hidden cameras recorded the customers entering their PINs, providing the criminals with complete card data.
- Cloning Cards: The criminals created counterfeit credit and debit cards with stolen card information, effectively replicating the original cards.
- Unauthorized Transactions: The cloned cards were used to make unauthorized purchases, cash withdrawals, and large bets at various locations, both within and outside of Las Vegas. This allowed the fraudsters to exploit the stolen data before being detected.
- Investigation and Arrests: As the unauthorized transactions mounted, several victims reported fraudulent activity to their banks and law enforcement. This led to a joint investigation involving local police, federal agencies, and casino security teams. The investigation eventually identified the skimming operation and the individuals behind it.
- Convictions: In 2008, federal authorities arrested several members of the criminal group involved in the Operation Get Rich or Die Tryin. The perpetrators faced charges of conspiracy, identity theft, and fraud. They were subsequently convicted and sentenced to lengthy prison terms.
How To Spot It?
To spot skimming fraud, individuals should remain vigilant and aware of potential signs that their card information may be at risk. To achieve, this:
- Regularly reviewing bank and credit card statements for unauthorized or suspicious transactions is essential, and any unusual activity should be reported to the bank or card issuer immediately.
- Physically checking devices can often reveal any hidden implants. If there is anything out of the ordinary about the way the card reader looks, it is better to conduct an inspection.
- Individuals should report any suspected skimming incidents to the establishment or business owner, as well as notify local authorities and their bank.
By adopting these measures, one can reduce the risk of falling victim to skimming fraud and protect their financial information from unauthorized access.
How To Prevent?
Preventing skimming fraud involves taking proactive measures to safeguard card information and stay vigilant against potential threats. Here are some effective steps to prevent skimming fraud:
- Inspect Card Readers: Before using an ATM, gas pump, or payment terminal, visually inspect the card reader for any signs of tampering or suspicious devices. Look for anything that seems out of place or different from the usual appearance.
- Use Secure ATMs and Payment Terminals: Use ATMs and payment terminals located in well-lit and secure areas. Avoid standalone or remote devices that may be more vulnerable to skimming attempts.
- Protect Your PIN: Always cover the keypad when entering the PIN to prevent hidden cameras or onlookers from capturing it.
- Use Contactless Payments: Consider using contactless payment methods, such as mobile wallets or contactless cards, whenever possible. These transactions use encryption and tokenization, making them more secure against skimming attempts.
- Enable Transaction Notifications: Set up transaction notifications on the mobile device or through the bank's app. These alerts will inform a person immediately of any card transactions, helping them spot unauthorized activities promptly.
- Regularly Review Statements: Review the bank and credit card statements to ensure all transactions are legitimate. If a person spots any suspicious or unauthorized charges, they should report them to the bank or card issuer immediately.
- Use Chip-Enabled Cards: It is better to use EMV chip-enabled cards instead of magnetic stripe cards. Chip technology provides better security and is more challenging for criminals to clone.
Disclosure: This article contains affiliate links. If you sign up through these links, we may earn a small commission at no extra cost to you.
Frequently Asked Questions (FAQs)
Skimming is generally considered illegal, as it involves the unauthorized collection of personal or financial information from individuals' payment cards. It's a form of fraud and is subject to legal consequences.
Skimming is a type of financial crime where unauthorized individuals use devices or techniques to collect personal or financial information from credit cards, debit cards, or other payment cards without the cardholder's knowledge or consent. The information collected through skimming can then be used for fraudulent purposes, such as making unauthorized purchases or withdrawing funds from the victim's account.
Financial skimming, also known simply as skimming, is a form of criminal activity in which individuals use various methods to capture and steal personal and financial information from payment cards, such as credit and debit cards. Skimming devices can be placed on legitimate card readers, like ATMs or gas pumps, or criminals may use handheld devices to directly swipe or capture card information.
Recommended Articles
This article has been a guide to Skimming Fraud and its meaning. Here, we explain its examples, how to prevent it, its types, and how to spot it. You may also find some useful articles here -