Table Of Contents
Phishing Meaning
Phishing is internet fraud that involves claiming to be a credible source to fool individuals into giving up sensitive data, like credentials or credit card information. It aims to deceive people or steals someone's identity. Scammers use E-mail, social media, and fraudulent websites for scamming.
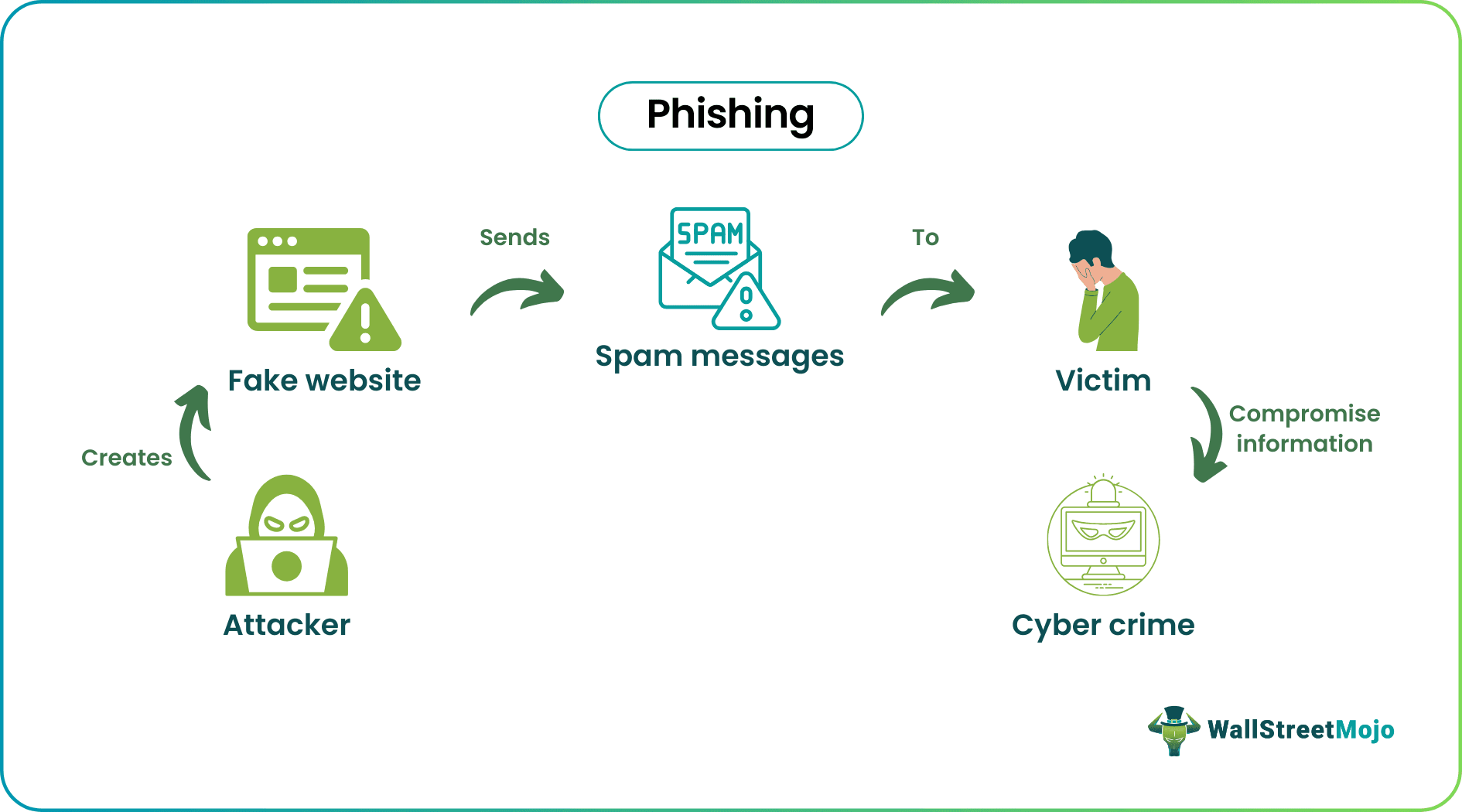
It aims to cheat people by appearing to be an authentic organization to persuade them to divulge sensitive information, including passwords, banking, credit card information, and personally identifiable information. Scammers subsequently utilize the data to access crucial accounts, which may lead to identity fraud and loss of money.
Table of contents
- Phishing Meaning
- Phishing is a form of data theft that asks people for personal details via emails, text messages, and calls.
- It is done to deceive people by asking them to disclose their credit card details, account numbers, or passwords. Phishing attacks may use a webpage, email, or other means of communication that appear to be legitimate.
- It can be avoided by cross-checking the authenticity of such messages and calls. For example, to trick people into entering their real credentials on a malicious website, websites might look precisely like legitimate websites.
How Does Phishing Work?
Phishing refers to data theft attacks or frauds through messages that appear to be from reliable business sources or websites. A link directs the visitor to a phony website that mimics the actual one and is typically included in a phishing email. The scammers prompt the users to submit personal data, including their credit card details. In addition, they frequently persuade the victim to divulge private information on a fraudulent website.
Scammers frequently use it as a launching pad into business or government networks, such as an advanced persistent threat incident, as part of the attack. In the latter case, they hack the data to overcome security barriers, spread malware within a secure environment, or obtain access to protected data.
In addition to suffering significant financial losses, a company that is the victim of such an attack frequently has its market share, reputation, and customer confidence decline. A security crisis from which an organization will have trouble recovering could result from such an attempt, depending on its breadth.
Choosing a reliable web hosting provider with strong security infrastructure, like Hostinger, can play a vital role in reducing cyber risks and ensuring data protection.
Detection
One may detect such scams in many ways. Let us discuss them in the following section.
- Misspelled Domain Name - Failing domain names and email addresses is simple. Therefore, one must verify the domain name of suspicious emails for spelling mistakes. One must always double-check messages, even if one receives them from a dependable sender.
- Suspicious Attachments And Links - Before one click or downloads an extension, hover over it to see whether there is a phishing link. One must refrain from clicking on the hyperlink if one is doubtful of the sender.
- Messages Asking For Urgent Response - Phishing scams intimidate victims into scaring tactics like urgency and authority. Therefore, emails that request information or financial transactions are suspicious.
- Messages From Public Email – Since no organization uses a public domain to message or mail its users, verifying the sender's mail is advisable.
- Poorly Written Email - The scammer's writing skills could be better. Knowing this makes it much simpler to distinguish between fraud and a mistake made by a reliable sender. Scammers frequently use an autocorrect feature or translation tool to create messages, providing them with all the necessary words but sometimes in a different context.
Many traders use Saxo Bank International to research and invest in stocks across different markets. Its features like SAXO Stocks offer access to a wide range of global equities for investors.
How To Prevent?
Some of the important ways to avoid it are as follows.
- Use Security Software – Users must use security software to avoid scams. In addition, it provides security to the devices and their software.
- Use Multi-Factor Authentication – Multi-factor authentication ensures multi-layer protection of the user's device.
- Timely Update Of The Device – Always update the device and software to avoid bugs that could find a place to creep in.
- Cross-Check Domain Name, Attachments, And Links – Verify the domain name, messages, and connections before responding or sharing personal information.
Types
Some of the popular types of it are the following:
- Angler Phishing – Here, scams are made possible by the volume of people complaining to companies directly on social media. Scammers are skilled at stealing responses and requesting personal information from the target. Fraudsters appear to be doing this to make it easier to receive compensation. Still, their real goal is to have their accounts compromised.
- Smishing And Vishing - Vishing includes a phone call, while smishing involves crooks sending text messages. Messages purporting to be from a bank warning one of unusual behavior are among the most popular smishing pretexts. The notice alleges that one is a scam victim and instructs one to click a link to stop future harm. The recipient is instead taken to a website run by the scammer and intended to record their banking information.
- Whaling - Whaling emails frequently include the excuse that the CEO is overworked and needs an employee to perform them a favor. Emails like the one above may not be as complex as spear-phishing emails, but they prey on workers' eagerness to obey their boss's orders. The sender may misbehave, yet the recipients may be suspicious of something but reluctant to approach them.
- Spear Phishing - Refers to malicious emails directed at a particular individual. Criminals who carry out this type of crime already know the victims' names, job descriptions, email addresses, and specifics of their job position.
- Email Phishing - Email is the primary tool for such scams. The fraudster will register a bogus domain that impersonates a legitimate business and submit thousands of boilerplate requests. The fake domain frequently uses character substitution, such as creating the word "rn" instead of the letter "m" by placing the letters "r" and "n" close to one another.
Examples
Let us understand it through the following examples.
Example #1
Suppose Michael receives a text message asking to change their bank account password to prevent scams with an attached link. The scammers will prompt Michael to do so without verifying the email's authenticity. The bank does not generate such messages or links. Responding to such mail can cause fall victim prey to online fraud. Such types of scams are known as smishing. One should always cross-check such messages with the sender.
Example #2
In December 2022, bogus purchasers defrauded at least 1,115 victims, causing them to lose at least $1 million. On the online marketplace Carousell, more people fell victim to scams than ever before and lost more money in December alone than in all of the months of the year combined. Carousell has also made steps to offer a required warning page whenever any non-Carousell hyperlink is introduced in a chat by a user.
Difference Between Spam And Phishing
Phishing is a cyberattack in which people are tricked into divulging their details, such as personal data, bank account information, credit card information, account passwords, and more, by the attacker using emails, texts, or phone calls that appear to be from a reliable source or company.
Spam is unsolicited emails frequently distributed in bulk to many recipients to propagate malware, carry out such attacks, or distribute advertisements.
Some of the critical differences between the two are:
| Phishing | Spam |
|---|---|
| It begins with a trap that appears to be authentic. | These are unsolicited emails flooding the inbox. |
| Harmful | Irritating |
| Includes all text messages and social media messages. | It also has commercial ads in the form of emails. |
Phishing vs Smishing vs Vishing
Phishing is a cyberattack technique that seeks to dupe users into clicking on phony email links. Similarly, smishing is a fraud that uses text messages instead of emails. At the same time, Vishing refers to fraudulent calls or voicemails.
Some of the essential differences between them are:
| Basis | Phishing | Smishing | Vishing |
|---|---|---|---|
| Strategies used | Includes emails | Includes text messages | Includes calls |
| Environment | Public mails | Private | Private |
| Virus | It is inserted in hyperlinks. | It may be inserted into messages | No such threats |
Disclosure: This article contains affiliate links. If you sign up through these links, we may earn a small commission at no extra cost to you.
Disclosure: This article contains affiliate links. If you sign up through these links, we may earn a small commission at no extra cost to you.
Frequently Asked Questions (FAQs)
A subject line with a phrase or word that doesn't sound appropriate is the most blatant sign of a dubious email.
It is prohibited whenever a regular citizen carries it out. However, it would be legal if done as part of a mission to intercept or infiltrate enemy data.
It is a form of social engineering in which a sender makes phony emails purporting to be from a reliable and trustworthy source.
Send any suspicious emails received to reportphishing@apwg.org so they can be investigated. At ReportFraud.ftc.gov, one can inform the FTC about the unwanted effort.